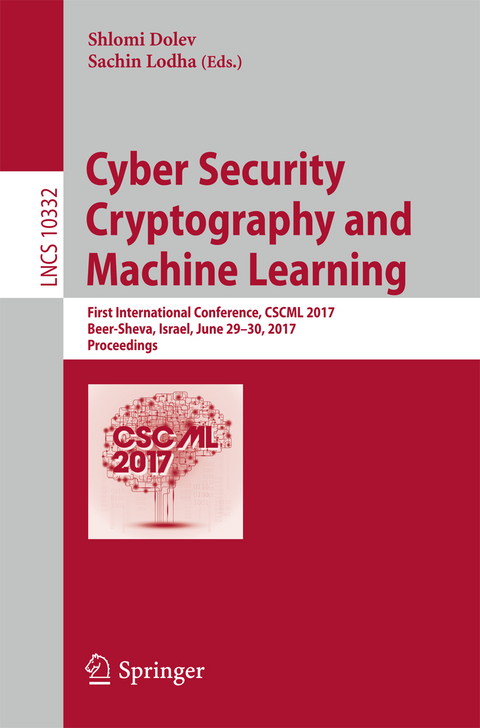
Cyber Security Cryptography and Machine Learning
Springer International Publishing (Verlag)
978-3-319-60079-6 (ISBN)
This book constitutes the proceedings of the first International Symposium on Cyber Security Cryptography and Machine Learning, held in Beer-Sheva, Israel, in June 2017.
The 17 full and 4 short papers presented include cyber security; secure software development methodologies, formal methods semantics and verification of secure systems; fault tolerance, reliability, availability of distributed secure systems; game-theoretic approaches to secure computing; automatic recovery of self-stabilizing and self-organizing systems; communication, authentication and identification security; cyber security for mobile and Internet of things; cyber security of corporations; security and privacy for cloud, edge and fog computing; cryptography; cryptographic implementation analysis and construction; secure multi-party computation; privacy-enhancing technologies and anonymity; post-quantum cryptography and security; machine learning and big data; anomaly detection and malware identification; business intelligence and security; digital forensics; digital rights management; trust management and reputation systems; information retrieval, risk analysis, DoS.lt;p>Cyber security.-Secure software development methodologies, formal methods semantics and verification of secure systems.-Fault tolerance, reliability, availability of distributed secure systems.- Game-theoretic approaches to secure computing.- Automatic recovery of self-stabilizing and self-organizing systems.- Communication, authentication and identification security.- Cyber security for mobile and Internet of things.- Cyber security of corporations.- Security and privacy for cloud, edge and fog computing.-Ccryptography.- Cryptographic implementation analysis and construction.- Secure multi-party computation.- Privacy-enhancing technologies and anonymity.- Post-quantum cryptography and security.- Machine learning and big data.- Anomaly detection and malware identification.- Business intelligence and security.- Digital forensics.- Digital rights management; trust management and reputation systems.- Information retrieval, risk analysis, DoS.>
| Erscheinungsdatum | 06.07.2017 |
|---|---|
| Reihe/Serie | Lecture Notes in Computer Science | Security and Cryptology |
| Zusatzinfo | XII, 307 p. 59 illus. |
| Verlagsort | Cham |
| Sprache | englisch |
| Maße | 155 x 235 mm |
| Gewicht | 492 g |
| Themenwelt | Informatik ► Netzwerke ► Sicherheit / Firewall |
| Schlagworte | algorithms • Applications • Artificial Intelligence • artificial intelligence (incl. robotics) • authentication • classification • computer crime • Computer Imaging, Vision, Pattern Recognition and • computer operating systems • computer programming languages • Computer Science • Computer Security • computer vision • conference proceedings • cybersecurity • data encryption • data privacy • Data Security • Discrete Mathematics • Discrete mathematics in computer science • Encryption • face recognition • Image Processing • Informatics • Internet • machine learning • malwares • Maths for computer scientists • Network Security • privacy • Research • Robotics • security • Signal Processing • Support Vector Machines (SVM) • systems and data security |
| ISBN-10 | 3-319-60079-6 / 3319600796 |
| ISBN-13 | 978-3-319-60079-6 / 9783319600796 |
| Zustand | Neuware |
| Haben Sie eine Frage zum Produkt? |
aus dem Bereich